CATEGORIES
Activities CentinelBox
Clients & Projects CentinelBox
Products & Services SAP
Products & Services CentinelBox
Tips CentinelBox
Request a FREE demonstration
We are CentinelBox, the best solution to manage the security of your SAP ERP system.
SAP Security: Controlling Critical Variables
May 31, 2023
What should I control? What are the critical variables in SAP security that I should monitor?
For executives and CISOs, a red alert is a first level to act upon. As we presented in the previous email, CentinelBox provides reports with color identification in cases where action is required… without the need for a deep understanding of the problem or its depth.
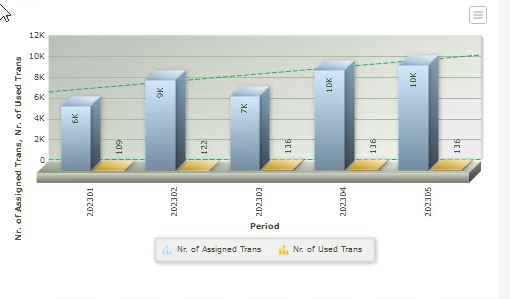
Along with these reports, graphical charts immediately show an indication of the security status:
Comparison between assigned and used transactions: a proper assignment should have a gap of 5 to 10% between the two values. Otherwise, there is a problem.
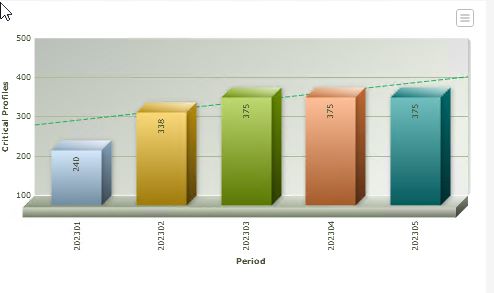
Critical variables:
User accounts with critical profile assigned: it should display zero!
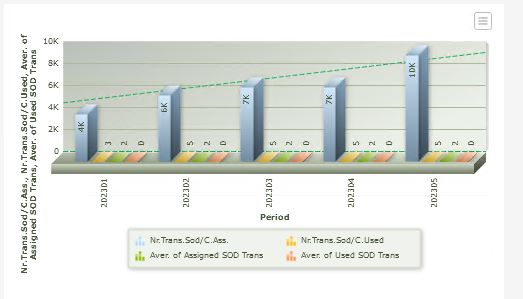
Comparison of assigned roles and used roles: both values should be similar with little variation (between 5 and 10%). Otherwise, we are in a scenario of role over-assignment, indicating privileges that users are not using.

Comparison of the number of conflicts related to segregation of duties between the quantity of assigned transactions and the transactions actually used. These values should be similar with little variation (between 5 and 10%). The primary cause could be attributed to role and transaction over-assignment, as presented in the previous charts.
At a second level, your alarms for conflicting SOD (Segregation of Duties) functions and critical functions provide analysis and evaluation information for auditors.
Want to learn more about CentinelBox and how we can help you take control of your SAP Security?
Schedule a personalised demo directly with me so you can see how our platform enables assertive and successful internal control.
Leave a Reply Cancel reply
Australia
Luo & Mont'YA IT Services
72 Woodlands Drive, Rochedale South, 4123
+61 403 286 968
Contact: Hernan Montoya
© 2024 CentinelBox. All rights reserved
Chile
TwoBox Ing. De Sistemas
contact@centinelbox.com
(569) 3202 7181
Perú
ATIQ Consultoría
www.atiqconsultoria.com
Info@atiqconsultoria.com
+51 932 266 090
México
www.centinelbox.mx
contact@centinelbox.mx
+52 1 55 1798 5870